Know the best cybersecurity strategies for small businesses; starting a small business is an exciting time. Three lattes, a flurry of meetings and clients, the novel feeling of knowing you’re doing something, and the rewards of being your own boss and living your dreams are countless.
What small business cybersecurity really means
Cybersecurity is the process of protecting your business systems, accounts, data, website, devices, and people from digital threats.
For a small business, that usually means protecting:
- Email accounts.
- Website admin panels.
- Customer information.
- Payment systems.
- Business documents.
- Employee devices.
- Cloud storage.
- Social media accounts.
- Accounting tools.
- Online store platforms.
- WiFi networks.
- Vendor and freelancer access.
Small business security should be practical. You do not need to build an enterprise security department on day one. You need to know what matters most, protect it first, and improve over time.
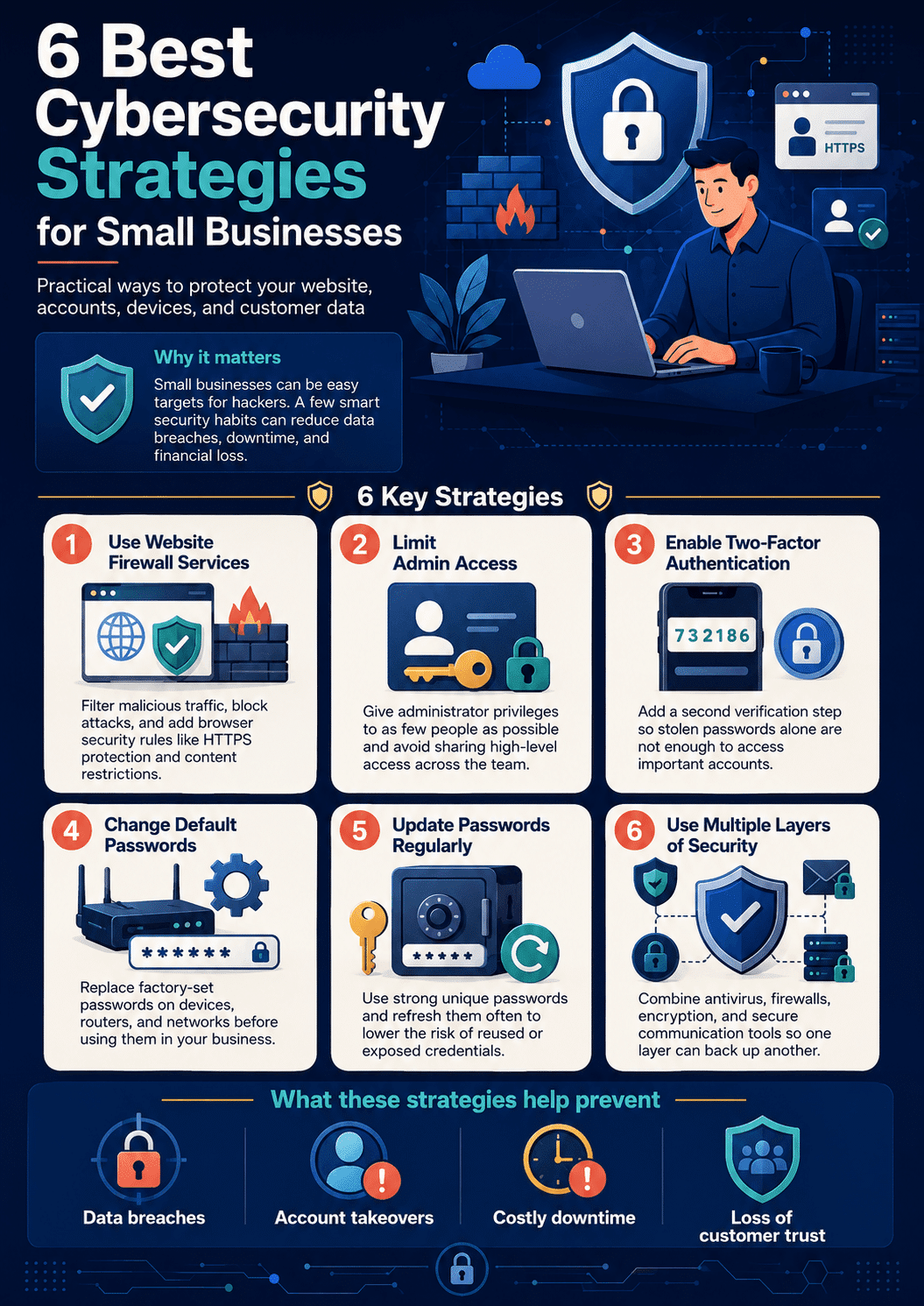
6 Best Cybersecurity Strategies for Small Businesses
But what also comes with it is loads of responsibilities, ranging from creating content for your marketing campaigns to filing quarterly taxes. And one responsibility that often falls off entrepreneurs’ radars is cybersecurity; especially when talking about tiny businesses with limited budgets and resources.
Let’s say you have a website where people come to buy cryptocurrency. There are chances they may purchase cryptocurrency directly, through a broker, or buy crypto with a credit card. Or have come to just convert cryptocurrency into their desired fiat currency. If a cybersecurity threat arises here, the hacker can harm your business and steal your customers’ credit card information.
So if you don’t think you need to worry about cybersecurity yet (or ever), please know it’s vital to protect your business from data breaches, hackers, and other cyber threats before they happen. Doing so could mean the difference between remaining in business or going under after an attack hits.
Cybersecurity Strategies for Small Businesses
Start with the accounts that can cause the most damage
Not every account carries the same risk.
A hacked newsletter account is a problem. A hacked business email, website admin account, payment platform, hosting account, or cloud storage account can become a disaster.
Before buying new security tools, list the accounts that control your business.
Start with:
- Website hosting.
- Domain registrar.
- WordPress admin account.
- Business email.
- Payment processor.
- Accounting software.
- Cloud storage.
- Social media accounts.
- Customer relationship management software.
- Admin accounts for online tools.
These accounts should have strong passwords, MFA, limited access, and recovery options that are kept up to date.
This one step makes the rest of your cybersecurity plan much easier.
Use Website Firewall Services
Website firewalls are a type of web security software that helps protect your website from attacks. They monitor for malicious or unwanted traffic and block it, which can help keep your site secure. You can also use website firewalls to enforce browser security rules like the ones listed below:
- Browsers will not allow JavaScript or Flash content to run on pages that are not SSL encrypted with HTTPS.
- Browsers will only load images from servers specifically whitelisted by their owner (you). So, this makes it harder for an attacker to change imagery on your site without permission.
Limit Access to Administrator Accounts
We’ve said a lot about how to secure your company’s networks and digital assets. Now, let’s talk about the people who should be using them.
First things first: Don’t use the same password for admin and user accounts. So, this is especially true if you’re using an easy-to-remember password for all of your employees’ accounts, and you probably are if you’re not taking steps to ensure that they use strong passwords themselves.
If one person’s account gets hacked by an attacker, he or she can easily access other employees’ accounts too.
Second: Limit access to administrator accounts to as few people as possible (ideally just one person). So, that way, even if someone gains access to an admin account by hacking into it or guessing its password; they won’t have access to everything else on the network because other people only have limited permissions in their user accounts.
Use Two-Factor Authentication
Two-factor authentication is often cited as one of the most effective cybersecurity strategies for small businesses. It works by requiring a second form of identification from you in order to log into your account or verify the information before granting access, such as by sending a code via text message or entering it into a physical key fob.
This type of security system helps prevent malicious actors from accessing your accounts even if they have stolen or guessed your password because now they need that second form of identification in addition to knowing the original password.
If someone steals your username and password but can’t get past two-factor authentication, they don’t have full access to your account. With this system, your data will remain safe, regardless of what other precautions you take against cyberattacks (antivirus software or firewalls); however, you should perform attack surface monitoring continuously to see if anyone is still trying to access it.
How do I set up two-factor authentication?
There are multiple ways to set up two-factor authentication depending on how secure you want your system to be: using external apps, generating codes with an authenticator app like Google Authenticator (available on both Android and iOS), sending codes via text messages when logging in using one of these authenticator apps at home.
Setting up a physical key fob connected directly to your computer’s USB port that generates codes every few seconds after inserting it into this port; setting up biometric sensors like fingerprint readers on laptops; so only those who have been verified through their fingerprints can use them; etc.
Change Default Passwords on Equipment and Networks
Therefore, this is a simple but effective way to protect your account. If you are using devices or networks, be sure to change the default password before using them. Most people don’t know this, but it’s easy to find default passwords online.
So if you don’t change your equipment’s defaults, someone else could easily access it and steal information or cause other problems with it.
So, it may sound scary at first, but with the help of a password manager and/or generator; changing a device password is very easy. Just be sure not to use something that’s too obvious—that would defeat the whole purpose!
Regularly change all your passwords for small business cybersecurity
Regularly changing your passwords is a must for protecting your business from hackers. The reason? Your computer’s memory can be read by a hacker, who then uses the information to guess your password. As long as you’re using the same password for multiple accounts and devices, that person can easily access all of them.
It’s important to change passwords on a regular basis as well; if you don’t, it becomes easier for someone else to do so later on. To avoid this happening in the first place, use strong passwords with letters (upper and lower case), numbers, symbols, and spaces between words.
So, you may also want to consider using an app like 1Password or LastPass that allows users to make changes across different sites at once instead of manually logging in to each one individually when updating credentials via email verification codes sent through text messages or phone calls, which only work so well since not everyone has reliable service these days anyway!
Use Multiple Layers of Security: Small Businesses Cybersecurity
Protecting a small business can require different approaches than protecting a large enterprise. The latter has more resources, both monetary and personnel-wise available to spend on cybersecurity, increasing the likelihood of success in preventing cyberattacks. However, as a small business, you can take some additional measures as well.
Using multiple layers of security is one of them. This means using two or more separate types of protection (such as antivirus software, firewalls, and encryption) to help protect your network against attacks. In addition, implementing different kinds of security measures ensures that if one layer fails, others will still be able to provide protection against potential threats.
You can strengthen this approach by switching to secure communication tools. Adopting encrypted email services like Atomic Mail, designed to send anonymous emails and protect data with zero-access encryption, will help you reduce exposure to phishing, spoofing, and unauthorized access.
Cybersecurity Strategies Small Businesses: In Conclusion
Cybersecurity is a critical threat to your business and can have devastating consequences. It is important to have a plan for dealing with security breaches and other cyber threats. Therefore, the best way to stay ahead of the times is to act proactively.
Take steps now so that you can prepare for what’s next down the road.
FAQ
Small businesses handle customer data, payments, email accounts, websites, business files, and financial records. Attackers may target them because they often have weaker security than larger companies.
Start by protecting important accounts with MFA, especially business email, website admin accounts, hosting, payment processors, and cloud storage.
Common threats include phishing, stolen passwords, ransomware, outdated software, fake invoices, website attacks, malware, insecure devices, and compromised vendor accounts.
Yes. MFA is one of the most practical ways to protect accounts, especially when passwords are stolen or reused.
Routine password changes are not always the best approach. It is better to use strong unique passwords, a password manager, and MFA. Change passwords when there is evidence of compromise or when someone leaves the business.
Important business data should be backed up automatically and regularly. The exact schedule depends on how often the data changes, but backups should also be tested.
Employees can help by spotting phishing, using strong passwords, reporting suspicious messages, avoiding unknown attachments, keeping devices updated, and following company security rules.
A website firewall can help block suspicious traffic and common attacks. It should be used together with updates, backups, secure hosting, MFA, and careful admin access.