
How to Detect and Avoid Phishing Attempts
Scammers and hackers often use malicious text messages and emails to deceive people and make them gi...
Explore all Visualmodo blog posts about Security, including content related to protection, surveillance, risk management, safeguards, defense, credentials, firewalls, protocols, and vulnerabilities. This tag archive brings together practical articles, guides, and insights to help readers discover security-related content focused on digital protection, access control, threat prevention, system safety, and best practices for reducing risk.

Scammers and hackers often use malicious text messages and emails to deceive people and make them gi...

In the constantly evolving world, there are more and more pieces of technology. That help us maintai...

Social media accounts are powerful tools for businesses and individuals alike. That's why more and m...

Are you worried that the internet will expose your data? Are you working with different files and in...

The dynamic application security testing (DAST) tools technique is one of the most important ways of...
Today more than half of the world’s population is online. What does this mean exactly? The figures...

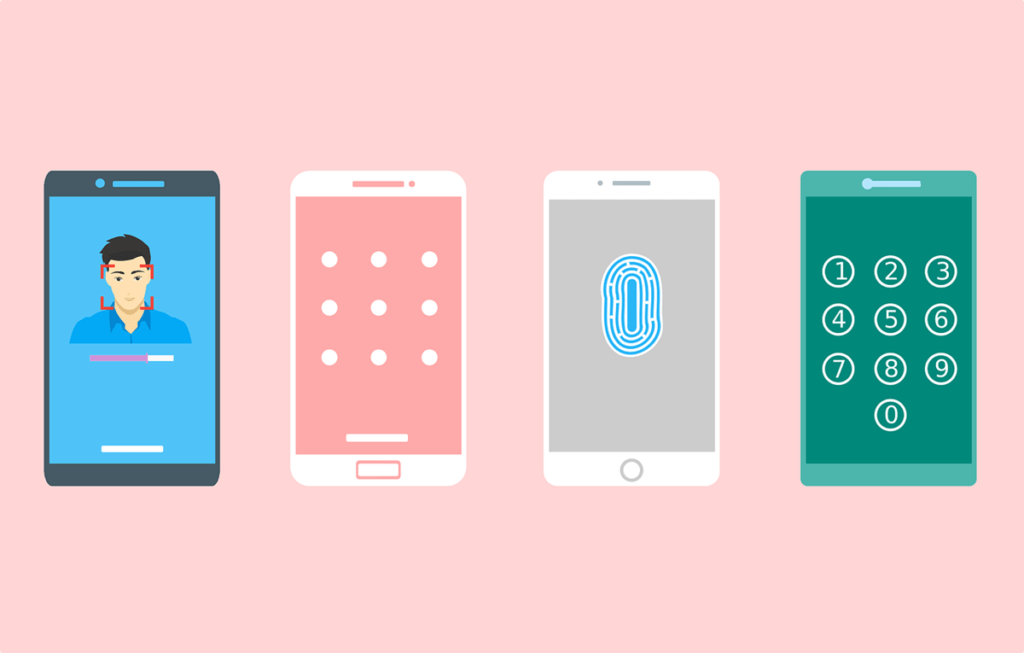
Principle-based access control technologies have been around for decades. They're one of the basic b...

It is a truly digital world. We are more connected than ever before. We store data in digital form, ...

Nowadays, nearly every business has a website. Because of this move towards online platforms, hacker...